The European Parliament fell victim to a DDoS cyberattack on Wednesday 23 November. Its site was taken out of service a few hours after a vote by MEPs describing Russia as a "State promoter of terrorism". The Speaker of Parliament tweeted that a pro-Kremlin group claimed responsibility for the attack, while Deputy Speaker Eva Kaili told the Politico website "strong reasons to believe that it is Killnet, Russian-Linked Hackers".
In France and in Europe, attacks of this kind against the sites of institutions or administrations are increasing. During the French presidential campaign of 2022, the cyberpirates of Killnet had already claimed to be at the origin of the breakdown of the site of Emmanuel Macron, denouncing "France's support for Ukraine". The group also claimed responsibility for a cyber attack on several Lithuanian government sites simultaneously in June: it was a reaction to the blocking of goods in the Kaliningrad enclave.
"This militant group was formed around March 2022, in response to Russia's invasion of Ukraine," says Gérôme Billois, cybersecurity expert at Wavestone, and author of the book Cyberattacks - The Underside of a Threat world. Killnet, which also paralyzed the sites of the Italian Senate, Norwegian administrations, Latvian public radio or the Czech government for a few hours, belongs to the category of "hacktivists". That is, hacker groups that carry out cyberattacks in the name of an ideology.
The group's specialty: DDoS, or "denial of service" attack. "It's a tool of medium intensity, which consists of blocking access to a website by saturating it with the number of connections. It's like a virtual demonstration, when thousands of people go to the same place" , explains the specialist. The consequences remain minor, since this type of attack does not cause long-term damage. "They cannot maintain it indefinitely, just as demonstrators cannot remain in the place they are blocking indefinitely: the connections cease after a while", explains Gérôme Billois.
Structured in a very volatile way, these groups of militant hackers do not have a fundamentally financial goal. "And they work by grouping together on Telegram channels, rallying sympathizers to be part of the attack and making their computer equipment available," says the expert. “Most of the targets are simply the actors who have implemented sanctions against Russia or made negative remarks, but also companies which have withdrawn from Russian territory, he explains. has also created a lot of concern among the companies concerned, which have invested in computer monitoring and protection cells.
More broadly, "according to government figures, cyberattacks have quadrupled in France" since 2020, says Gérôme Billois. Many of them are perpetrated by cybercriminal hacker groups, which are not militant but seek to obtain money through "ransomware" causing computer networks to be blocked and data theft. In recent months, the Corbeil-Essonnes hospital, the cities of Chaville (Hauts-de-Seine) or Caen (Calvados) as well as many companies have been victims. These groups operate "like real small cybercrime SMEs, with 10 to 60 employees, they hire attackers and distribute the ransoms", says Gérôme Billois.
One of the best-known groups, Lockbit, is also affiliated with Russia, although it claims to be apolitical. “Historically, many cybercriminal groups are based in Russian-speaking countries and enjoy a form of impunity when they are smart enough not to attack their own countries and companies. carry out attacks against the countries of the former USSR," he explains.
If these two types of groups operate according to different methods and with different motivations, "we must keep in mind that the world of piracy is very porous", recalls the cybersecurity specialist. “It is not impossible that ransomware groups are protected by states that use them to launch attacks, or that militant groups are joined and funded by state actors.”
 Poland, big winner of European enlargement
Poland, big winner of European enlargement In Israel, step-by-step negotiations for a ceasefire in the Gaza Strip
In Israel, step-by-step negotiations for a ceasefire in the Gaza Strip BBVA ADRs fall almost 2% on Wall Street
BBVA ADRs fall almost 2% on Wall Street Ukraine has lost 10 million inhabitants since 2001... and could lose as many by 2050
Ukraine has lost 10 million inhabitants since 2001... and could lose as many by 2050 Sánchez cancels his agenda and considers resigning: "I need to stop and reflect"
Sánchez cancels his agenda and considers resigning: "I need to stop and reflect" The Federal Committee of the PSOE interrupts the event to take to the streets with the militants
The Federal Committee of the PSOE interrupts the event to take to the streets with the militants Repsol: "We want to lead generative AI to guarantee its benefits and avoid risks"
Repsol: "We want to lead generative AI to guarantee its benefits and avoid risks" Osteoarthritis: an innovation to improve its management
Osteoarthritis: an innovation to improve its management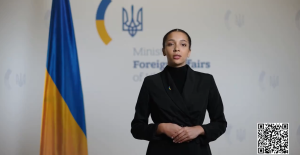 Ukraine gets a spokesperson generated by artificial intelligence
Ukraine gets a spokesperson generated by artificial intelligence The French will take advantage of the May bridges to explore France
The French will take advantage of the May bridges to explore France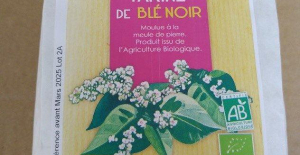 Organic flour contaminated by a recalled toxic plant
Organic flour contaminated by a recalled toxic plant 2024 Olympics: Parisian garbage collectors have filed a strike notice
2024 Olympics: Parisian garbage collectors have filed a strike notice Death of Paul Auster: Actes Sud says he is “lucky” to have been his publisher in France
Death of Paul Auster: Actes Sud says he is “lucky” to have been his publisher in France Lang Lang, the most French of Chinese pianists
Lang Lang, the most French of Chinese pianists Author of the “New York Trilogy”, American novelist Paul Auster has died at the age of 77
Author of the “New York Trilogy”, American novelist Paul Auster has died at the age of 77 To the End of the World, The Stolen Painting, Border Line... Films to watch this week
To the End of the World, The Stolen Painting, Border Line... Films to watch this week Omoda 7, another Chinese car that could be manufactured in Spain
Omoda 7, another Chinese car that could be manufactured in Spain BYD chooses CA Auto Bank as financial partner in Spain
BYD chooses CA Auto Bank as financial partner in Spain Tesla and Baidu sign key agreement to boost development of autonomous driving
Tesla and Baidu sign key agreement to boost development of autonomous driving Skoda Kodiaq 2024: a 'beast' plug-in hybrid SUV
Skoda Kodiaq 2024: a 'beast' plug-in hybrid SUV The home mortgage firm rises 3.8% in February and the average interest moderates to 3.33%
The home mortgage firm rises 3.8% in February and the average interest moderates to 3.33%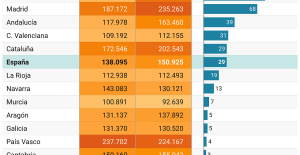 This is how housing prices have changed in Spain in the last decade
This is how housing prices have changed in Spain in the last decade The home mortgage firm drops 10% in January and interest soars to 3.46%
The home mortgage firm drops 10% in January and interest soars to 3.46% The jewel of the Rocío de Nagüeles urbanization: a dream villa in Marbella
The jewel of the Rocío de Nagüeles urbanization: a dream villa in Marbella Europeans: a senior official on the National Rally list
Europeans: a senior official on the National Rally list Blockade of Sciences Po: the right denounces a “drift”, the government charges the rebels
Blockade of Sciences Po: the right denounces a “drift”, the government charges the rebels Even on a mission for NATO, the Charles-de-Gaulle remains under French control, Lecornu responds to Mélenchon
Even on a mission for NATO, the Charles-de-Gaulle remains under French control, Lecornu responds to Mélenchon “Deadly Europe”, “economic decline”, immigration… What to remember from Emmanuel Macron’s speech at the Sorbonne
“Deadly Europe”, “economic decline”, immigration… What to remember from Emmanuel Macron’s speech at the Sorbonne These French cities that will boycott the World Cup in Qatar
These French cities that will boycott the World Cup in Qatar Top 14: Fijian hooker Narisia leaves Racing 92 and signs for Oyonnax
Top 14: Fijian hooker Narisia leaves Racing 92 and signs for Oyonnax Europa League: Jean-Louis Gasset is “wary” of Atalanta, an “atypical team”
Europa League: Jean-Louis Gasset is “wary” of Atalanta, an “atypical team” Europa League: “I don’t believe it…”, Gasset jokes about Aubameyang’s age
Europa League: “I don’t believe it…”, Gasset jokes about Aubameyang’s age Foot: Rupture of the cruciate ligaments for Sergino Dest (PSV), absent until 2025
Foot: Rupture of the cruciate ligaments for Sergino Dest (PSV), absent until 2025