The number is enormous: 2'692 818'238 lines with access data for Internet services appeared in the network. But millions of E-Mail addresses and passwords in the network unencrypted and so readable.
The IT security researcher Troy Hunt met during his research in a hacker forum on the data leak. It could, at times, to be there, and also on the Cloud service Mega download. The magazine "Wired" called it the biggest Leak, which was previously known to the public.
in terms of the Numbers a little bigger, the two in 2016, known Yahoo-Leaks, one of which, respectively, three billion records were affected would in theory. However, both of these sensitive records are not yet showed up in the publicly viewable part of the network.
22 million passwords published
Otherwise, the "Collection #1", such as the well known data set is named. The origin of the data is exactly, is still unclear. Hunt, according to a variety of Websites are affected. Apparently, the Publishing is concentrated in the collection of a variety of older and newer Leaks.
Hunt wrote in a blog post that it had detected some data, about 140 million E-Mail addresses were also new for him. He have been adjusted for the collection of duplicates-and-dirty records, then approximately 770 million E-Mail are still addresses left, 22 million passwords.
the difference between The two Figures is explained by the fact that many users use different than recommended the same password for more than one page. In addition, different users can happen to use identical passwords, which relates in particular to simple passwords such as "123456".
detours Hacker get account data
With the Leak of the millions of access data are now hackers from all over the world available to the users to spy or to try to get to Shopping and banking data. This happens in the case of such large Leaks often called a "credential stuffing", which translates roughly as "Stuff with logon data". In the process, hackers can fire very long lists with E-Mail-password combinations from automated access to a system of a service, for example on Spotify.
The Software tried independently, with hundreds of thousands of access data sequentially to log in. At this mass, the Chance is not too small to land with some of the combinations of hits and to gain access to user accounts. An analysis of the IT security company Shape Security in the summer of 2018, according to 80 percent of Log-in Attempts to shopping pages from Unauthorized. Almost on a par with the Figures for the web sites of airlines.
user check whether you are affected
"Collection #1"-explorers, Hunt is recognized among professionals as the expert for the security of login data. He has loaded the latest Leak in his database that he has collected since a few years, Leaks. To help Internet users to protect themselves: On its Website haveibeenpwned.com you can check whether you are affected by the current Leak, or older. To do this, you need to enter in the search field, type an E-Mail address for Log-ins.
After a click on the "search" checks the website, whether or not the E-Mail address showed up in one of the Leaks from the past few years. You are not only shows, in which Leak this E-Mail address showed up, however, which password was used – that would be a security problem.
a collection of data "Collection #1", is also not clear which web sites or Apps are affected. Your own data should be affected so, then users should change as soon as possible your passwords for all the services to which this E-Mail address. (Editorial Tamedia)
Created: 17.01.2019, 15:02 PM
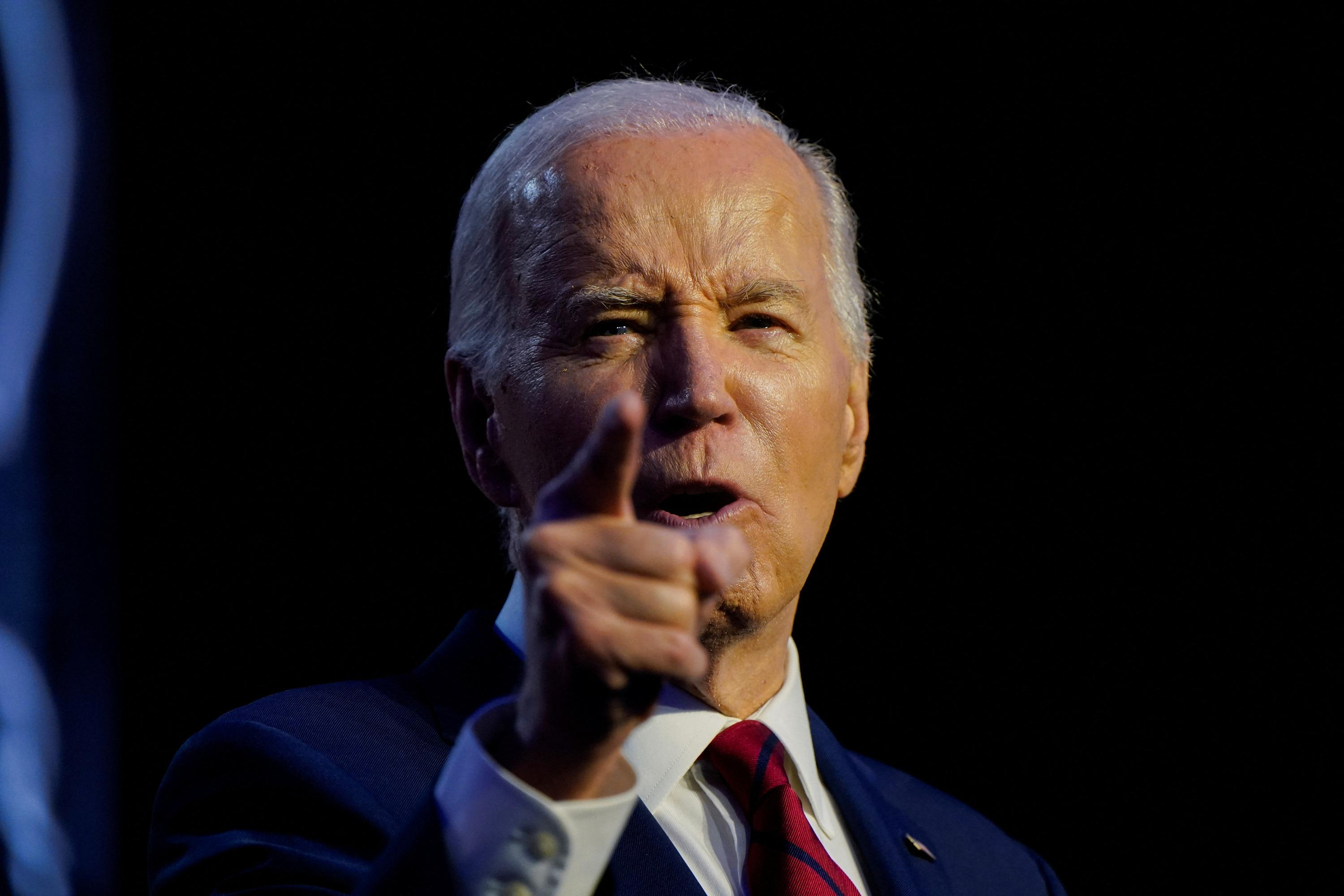
 United States: divided on the question of presidential immunity, the Supreme Court offers respite to Trump
United States: divided on the question of presidential immunity, the Supreme Court offers respite to Trump Maurizio Molinari: “the Scurati affair, a European injury”
Maurizio Molinari: “the Scurati affair, a European injury” Hamas-Israel war: US begins construction of pier in Gaza
Hamas-Israel war: US begins construction of pier in Gaza Israel prepares to attack Rafah
Israel prepares to attack Rafah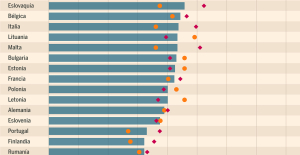 Spain is the country in the European Union with the most overqualified workers for their jobs
Spain is the country in the European Union with the most overqualified workers for their jobs Parvovirus alert, the “fifth disease” of children which has already caused the death of five babies in 2024
Parvovirus alert, the “fifth disease” of children which has already caused the death of five babies in 2024 Colorectal cancer: what to watch out for in those under 50
Colorectal cancer: what to watch out for in those under 50 H5N1 virus: traces detected in pasteurized milk in the United States
H5N1 virus: traces detected in pasteurized milk in the United States Private clinics announce a strike with “total suspension” of their activities, including emergencies, from June 3 to 5
Private clinics announce a strike with “total suspension” of their activities, including emergencies, from June 3 to 5 The Lagardère group wants to accentuate “synergies” with Vivendi, its new owner
The Lagardère group wants to accentuate “synergies” with Vivendi, its new owner The iconic tennis video game “Top Spin” returns after 13 years of absence
The iconic tennis video game “Top Spin” returns after 13 years of absence Three Stellantis automobile factories shut down due to supplier strike
Three Stellantis automobile factories shut down due to supplier strike A pre-Roman necropolis discovered in Italy during archaeological excavations
A pre-Roman necropolis discovered in Italy during archaeological excavations Searches in Guadeloupe for an investigation into the memorial dedicated to the history of slavery
Searches in Guadeloupe for an investigation into the memorial dedicated to the history of slavery Aya Nakamura in Olympic form a few hours before the Flames ceremony
Aya Nakamura in Olympic form a few hours before the Flames ceremony Psychiatrist Raphaël Gaillard elected to the French Academy
Psychiatrist Raphaël Gaillard elected to the French Academy Skoda Kodiaq 2024: a 'beast' plug-in hybrid SUV
Skoda Kodiaq 2024: a 'beast' plug-in hybrid SUV Tesla launches a new Model Y with 600 km of autonomy at a "more accessible price"
Tesla launches a new Model Y with 600 km of autonomy at a "more accessible price" The 10 best-selling cars in March 2024 in Spain: sales fall due to Easter
The 10 best-selling cars in March 2024 in Spain: sales fall due to Easter A private jet company buys more than 100 flying cars
A private jet company buys more than 100 flying cars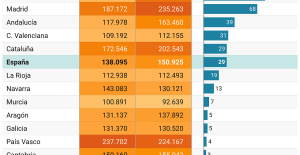 This is how housing prices have changed in Spain in the last decade
This is how housing prices have changed in Spain in the last decade The home mortgage firm drops 10% in January and interest soars to 3.46%
The home mortgage firm drops 10% in January and interest soars to 3.46% The jewel of the Rocío de Nagüeles urbanization: a dream villa in Marbella
The jewel of the Rocío de Nagüeles urbanization: a dream villa in Marbella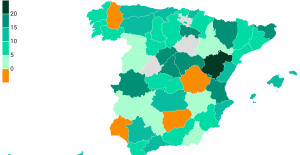 Rental prices grow by 7.3% in February: where does it go up and where does it go down?
Rental prices grow by 7.3% in February: where does it go up and where does it go down? Even on a mission for NATO, the Charles-de-Gaulle remains under French control, Lecornu responds to Mélenchon
Even on a mission for NATO, the Charles-de-Gaulle remains under French control, Lecornu responds to Mélenchon “Deadly Europe”, “economic decline”, immigration… What to remember from Emmanuel Macron’s speech at the Sorbonne
“Deadly Europe”, “economic decline”, immigration… What to remember from Emmanuel Macron’s speech at the Sorbonne Sale of Biogaran: The Republicans write to Emmanuel Macron
Sale of Biogaran: The Republicans write to Emmanuel Macron Europeans: “All those who claim that we don’t need Europe are liars”, criticizes Bayrou
Europeans: “All those who claim that we don’t need Europe are liars”, criticizes Bayrou These French cities that will boycott the World Cup in Qatar
These French cities that will boycott the World Cup in Qatar Archery: everything you need to know about the sport
Archery: everything you need to know about the sport Handball: “We collapsed”, regrets Nikola Karabatic after PSG-Barcelona
Handball: “We collapsed”, regrets Nikola Karabatic after PSG-Barcelona Tennis: smash, drop shot, slide... Nadal's best points for his return to Madrid (video)
Tennis: smash, drop shot, slide... Nadal's best points for his return to Madrid (video) Pro D2: Biarritz wins a significant success in Agen and takes another step towards maintaining
Pro D2: Biarritz wins a significant success in Agen and takes another step towards maintaining