"The care of patients is not endangered", indicated the Minister of Health, François Braun, on Tuesday during a visit to Montpellier, specifying that patients coming under "severe technical platforms" were " redirected by the Samu to other hospitals".
Same reassuring tone at the level of the management of the establishment where the situation was the same as the day before: the work is done "by hand, without the help of computers". "We are working in degraded mode, not for the patient, but for us," she told AFP.
The South Francilien Hospital Center (CHSF) in Corbeil-Essonnes, south-east of Paris, has been the victim of a computer attack since the night of Saturday to Sunday around 01:00. A ransom demand of 10 million dollars, formulated in English, was demanded by the hacker(s).
"It's a cyberattack as unfortunately there are in all establishments, (...) as there are regularly unfortunately. We will not give in", assured Mr. Braun.
In recent years, the number of cyberattacks has greatly increased and they no longer spare healthcare establishments, even if they are not necessarily a priority target.
In 2021, the National Authority for the Security and Defense of Information Systems (Anssi) noted on average one incident of this type per week in a health establishment in France.
“Hackers have particularly wide targets, they go fishing. It is essentially the lure of profit that motivates them, even if some may also have ideological motivations, revenge,” the general told AFP. Christophe Husson, second in command of the Cyberspace Gendarmerie Command (ComCyberGend), recalling that the "global cost of cybercrime is estimated at 6 billion dollars per year".
- "digital evidence" -
For a long time, "many threat actors had an unspoken rule to leave hospitals alone", underlines Fabien Rech of the American computer security company Trellix. “However, given the current deterioration of relations between Eastern and Western countries and the fact that a number of ransomware operators are affiliated with countries of the former USSR, we suspect that Western hospitals were put back on the target list."
The Paris prosecutor's office announced on Monday the opening of an investigation for intrusion into the computer system and attempted extortion by an organized gang, supervised by its cybercrime section. The investigations were entrusted to the gendarmes of the Center for the Fight against Digital Crime.
According to a source close to the investigation, the ransomware belongs to the Lockbit group. Around 100 affiliates participate in the group's activities, according to an interview cited recently by cybersecurity specialist Damien Bancal on his blog Zataz.com.
This galaxy of specialists revolves around a software, a common platform offering all the tools to carry out the attack. They collaborate together with professional methods and share the ransoms.
Lockbit is active worldwide (USA, China, India, Indonesia, Ukraine, France, UK, Germany...) but seems to avoid attacking targets in Russia and CIS countries, probably "to avoid prosecution in these regions," according to cybersecurity firm Kaspersky. At the time of the Russian offensive in Ukraine, Lockbit made it known that it was "apolitical" and did not seek to meddle in the conflict.
The purpose of the cybergendarmes' investigation is to collect "digital evidence" to "identify the perpetrators, locate them and arrest them". These investigations are "always very long, can last several months or even several years" and require significant international cooperation, warns General Husson.
ysp-ol-tll-mk-lby-lc/cel/abl
 War in Ukraine: when kyiv attacks Russia with inflatable balloons loaded with explosives
War in Ukraine: when kyiv attacks Russia with inflatable balloons loaded with explosives United States: divided on the question of presidential immunity, the Supreme Court offers respite to Trump
United States: divided on the question of presidential immunity, the Supreme Court offers respite to Trump Maurizio Molinari: “the Scurati affair, a European injury”
Maurizio Molinari: “the Scurati affair, a European injury” Hamas-Israel war: US begins construction of pier in Gaza
Hamas-Israel war: US begins construction of pier in Gaza First three cases of “native” cholera confirmed in Mayotte
First three cases of “native” cholera confirmed in Mayotte Meningitis: compulsory vaccination for babies will be extended in 2025
Meningitis: compulsory vaccination for babies will be extended in 2025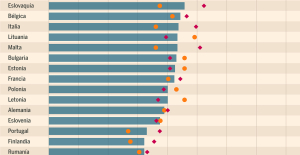 Spain is the country in the European Union with the most overqualified workers for their jobs
Spain is the country in the European Union with the most overqualified workers for their jobs Parvovirus alert, the “fifth disease” of children which has already caused the death of five babies in 2024
Parvovirus alert, the “fifth disease” of children which has already caused the death of five babies in 2024 Inflation rebounds in March in the United States, a few days before the Fed meeting
Inflation rebounds in March in the United States, a few days before the Fed meeting Video games: Blizzard cancels Blizzcon 2024, its annual high mass
Video games: Blizzard cancels Blizzcon 2024, its annual high mass Falling wings of the Moulin Rouge: who will pay for the repairs?
Falling wings of the Moulin Rouge: who will pay for the repairs? “You don’t sell a company like that”: Roland Lescure “annoyed” by the prospect of a sale of Biogaran
“You don’t sell a company like that”: Roland Lescure “annoyed” by the prospect of a sale of Biogaran Exhibition: in Deauville, Zao Wou-Ki, beauty in all things
Exhibition: in Deauville, Zao Wou-Ki, beauty in all things Dak’art, the most important biennial of African art, postponed due to lack of funding
Dak’art, the most important biennial of African art, postponed due to lack of funding In Deadpool and Wolverine, Ryan and Hugh Jackman explore the depths of the Marvel multiverse
In Deadpool and Wolverine, Ryan and Hugh Jackman explore the depths of the Marvel multiverse Tom Cruise returns to Paris for the filming of Mission Impossible 8
Tom Cruise returns to Paris for the filming of Mission Impossible 8 Skoda Kodiaq 2024: a 'beast' plug-in hybrid SUV
Skoda Kodiaq 2024: a 'beast' plug-in hybrid SUV Tesla launches a new Model Y with 600 km of autonomy at a "more accessible price"
Tesla launches a new Model Y with 600 km of autonomy at a "more accessible price" The 10 best-selling cars in March 2024 in Spain: sales fall due to Easter
The 10 best-selling cars in March 2024 in Spain: sales fall due to Easter A private jet company buys more than 100 flying cars
A private jet company buys more than 100 flying cars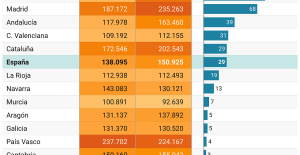 This is how housing prices have changed in Spain in the last decade
This is how housing prices have changed in Spain in the last decade The home mortgage firm drops 10% in January and interest soars to 3.46%
The home mortgage firm drops 10% in January and interest soars to 3.46% The jewel of the Rocío de Nagüeles urbanization: a dream villa in Marbella
The jewel of the Rocío de Nagüeles urbanization: a dream villa in Marbella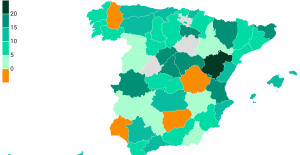 Rental prices grow by 7.3% in February: where does it go up and where does it go down?
Rental prices grow by 7.3% in February: where does it go up and where does it go down? Even on a mission for NATO, the Charles-de-Gaulle remains under French control, Lecornu responds to Mélenchon
Even on a mission for NATO, the Charles-de-Gaulle remains under French control, Lecornu responds to Mélenchon “Deadly Europe”, “economic decline”, immigration… What to remember from Emmanuel Macron’s speech at the Sorbonne
“Deadly Europe”, “economic decline”, immigration… What to remember from Emmanuel Macron’s speech at the Sorbonne Sale of Biogaran: The Republicans write to Emmanuel Macron
Sale of Biogaran: The Republicans write to Emmanuel Macron Europeans: “All those who claim that we don’t need Europe are liars”, criticizes Bayrou
Europeans: “All those who claim that we don’t need Europe are liars”, criticizes Bayrou These French cities that will boycott the World Cup in Qatar
These French cities that will boycott the World Cup in Qatar Basketball: Strasbourg appeals the victory recovered by Monaco
Basketball: Strasbourg appeals the victory recovered by Monaco Top 14: UBB with Tatafu and Moefana against Bayonne
Top 14: UBB with Tatafu and Moefana against Bayonne MotoGP: Bagnaia dominates qualifying practice in Spain and sets track record
MotoGP: Bagnaia dominates qualifying practice in Spain and sets track record Olympic Games: in Athens, Greece transmits the Olympic flame to France
Olympic Games: in Athens, Greece transmits the Olympic flame to France