"A cybersecurity incident". This is how Uber reported a hack on the night of September 15-16. The American company of VTC revealed more information on this cyberattack, publishing on its site, Monday evening, September 19, a first report returning to this intrusion and this data leak of which it was the victim.
Uber attributes the attack to the cybercriminal group Lapsus$. This group of South American hackers, active since the end of 2021, was particularly offensive at the beginning of 2022, claiming in particular the hacking of Microsoft, Okta, Nvidia and Samsung, before several arrests in the United Kingdom. in April bring a halt to these pirates. Lapsus$'s communication methods are somewhat particular, as mentioned by 01net.com. Everything is indeed happening in a Telegram channel, with unorthodox claims.
As Le Monde reports, Uber believes that the techniques that allowed hackers to compromise its system are similar to those previously employed by Lapsus$. The hack came to light after a message from the malicious hacker leaked on one of the company's Slack channels - an online collaborative platform. The attacker(s) then reconfigured Uber's OpenDNS - the service allowing automatic corrections of domain names entered by the user as well as a service blocking certain categories of domain names - to display an image to employees. on some internal sites.
According to the New York Times and cybersecurity experts, a hacker who says he is 18 obtained access codes to Uber's internal network by texting an employee of the firm claiming to be a member of the IT staff of Uber. company, which persuaded him to reveal his password. However, as ZDNet.com reports, Uber clarified on Monday that the hacker(s) gained access using the credentials of a third-party contractor. "It is likely that the attacker bought the contractor's Uber password on the Dark Web," said the American company, after the contractor's personal device was infected with malware.
Uber says that the attacker(s) then managed to bypass multi-factor authentication by multiplying connection attempts until the victim mistakenly validated the authentication request. Then, inside the system, the attacker(s) targeted the accounts of other users, until they reached a level of privilege high enough to access corporate resources.
In its report, Uber also gives an estimate of the data stolen by the perpetrator(s) of the attack. The chauffeur-driven vehicle booking platform found that messages posted on its internal Slack had been downloaded, as well as information available through the software used by the accounting team to process invoices. Uber, however, says the group of hackers does not appear to have infiltrated publicly accessible systems, user accounts or databases storing sensitive user information, such as payment data.
Uber also notes that the hack that targeted Rockstar Games on Sunday, the publisher of the famous video game Grand Theft Auto (GTA) 6, follows a similar pattern. Rockstar Games has admitted that videos of the next version of the cult saga, currently in development, were pirated and posted online this weekend.
“We recently experienced a computer breach in which an unauthorized third party illegally accessed and downloaded confidential information on our systems, including images from the upcoming Grand Theft Auto,” the studio tweeted.
The specialized site PC Gamer noted that a file containing some 90 videos of GTA 6 was published on forums of players. The person who posted them under the pseudonym "teapotuberhacker" then claimed to be also responsible for the Uber hack last week and promised to "leak more information soon" about the game.
The videos notably show a new female character that players could choose from. The Bloomberg agency had indicated earlier this year that GTA 6 should feature a female protagonist influenced by the mythical American couple Bonnie and Clyde.
 Sudan ravaged by a year of war
Sudan ravaged by a year of war Ten years after the kidnapping of the Chibok girls, what has become of the terrorist group Boko Haram?
Ten years after the kidnapping of the Chibok girls, what has become of the terrorist group Boko Haram? The Israeli government divided on the extent of its response after Iran's direct attack on its territory
The Israeli government divided on the extent of its response after Iran's direct attack on its territory “Is it time for a killing blow?” : the Israeli press wonders about a response after the Iranian attack
“Is it time for a killing blow?” : the Israeli press wonders about a response after the Iranian attack Covid-19: everything you need to know about the new vaccination campaign which is starting
Covid-19: everything you need to know about the new vaccination campaign which is starting The best laptops of the moment boast artificial intelligence
The best laptops of the moment boast artificial intelligence Amazon invests 700 million in robotizing its warehouses in Europe
Amazon invests 700 million in robotizing its warehouses in Europe Inflation rises to 3.2% in March due to gasoline and electricity bills
Inflation rises to 3.2% in March due to gasoline and electricity bills Large French companies are alarmed by the stalling of the European economy
Large French companies are alarmed by the stalling of the European economy New sanctions against Russia send industrial metal prices soaring
New sanctions against Russia send industrial metal prices soaring Olympic Games 2024: civil servants authorized to carry out private security activities
Olympic Games 2024: civil servants authorized to carry out private security activities Threat of strikes for the 2024 Olympics: Macron says he has “confidence” in the “spirit of responsibility” of the unions
Threat of strikes for the 2024 Olympics: Macron says he has “confidence” in the “spirit of responsibility” of the unions Musical show: “Come Bach”, fantasies around the composer
Musical show: “Come Bach”, fantasies around the composer The cry of alarm from Senghor's friends has been heard
The cry of alarm from Senghor's friends has been heard World Chess Championship: Nepomniachtchi and Gukesh lead the candidates tournament
World Chess Championship: Nepomniachtchi and Gukesh lead the candidates tournament Rapper Heuss L’Enfoiré calls on Ronaldinho for his new music video
Rapper Heuss L’Enfoiré calls on Ronaldinho for his new music video Skoda Kodiaq 2024: a 'beast' plug-in hybrid SUV
Skoda Kodiaq 2024: a 'beast' plug-in hybrid SUV Tesla launches a new Model Y with 600 km of autonomy at a "more accessible price"
Tesla launches a new Model Y with 600 km of autonomy at a "more accessible price" The 10 best-selling cars in March 2024 in Spain: sales fall due to Easter
The 10 best-selling cars in March 2024 in Spain: sales fall due to Easter A private jet company buys more than 100 flying cars
A private jet company buys more than 100 flying cars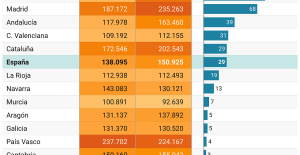 This is how housing prices have changed in Spain in the last decade
This is how housing prices have changed in Spain in the last decade The home mortgage firm drops 10% in January and interest soars to 3.46%
The home mortgage firm drops 10% in January and interest soars to 3.46% The jewel of the Rocío de Nagüeles urbanization: a dream villa in Marbella
The jewel of the Rocío de Nagüeles urbanization: a dream villa in Marbella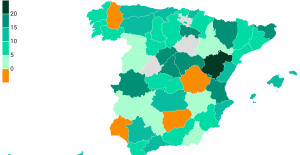 Rental prices grow by 7.3% in February: where does it go up and where does it go down?
Rental prices grow by 7.3% in February: where does it go up and where does it go down? Europeans: the schedule of debates to follow between now and June 9
Europeans: the schedule of debates to follow between now and June 9 Europeans: “In France, there is a left and there is a right,” assures Bellamy
Europeans: “In France, there is a left and there is a right,” assures Bellamy During the night of the economy, the right points out the budgetary flaws of the macronie
During the night of the economy, the right points out the budgetary flaws of the macronie Europeans: Glucksmann denounces “Emmanuel Macron’s failure” in the face of Bardella’s success
Europeans: Glucksmann denounces “Emmanuel Macron’s failure” in the face of Bardella’s success These French cities that will boycott the World Cup in Qatar
These French cities that will boycott the World Cup in Qatar Augusta Masters: the unchallenged reign of Scottie Scheffler
Augusta Masters: the unchallenged reign of Scottie Scheffler Tennis: Harold Mayot takes Cachin and goes to the second round in Barcelona
Tennis: Harold Mayot takes Cachin and goes to the second round in Barcelona Barça-PSG: “We will do it”, Luis Enrique shows his confidence before the return match
Barça-PSG: “We will do it”, Luis Enrique shows his confidence before the return match Hakimi on Mbappé before Barça-PSG: “I feel very good, very motivated, like the whole team”
Hakimi on Mbappé before Barça-PSG: “I feel very good, very motivated, like the whole team”